Understanding API Keys: Functionality, Use Cases, and System Behavior
APIs enable smooth communication between applications, services, and platforms, forming the backbone of many modern digital experiences.
From retrieving data to executing critical operations, APIs often expose sensitive information and core system functionality.
Without proper access control, these interfaces can be misused, overloaded, or exploited by unauthorised actors, leading to security risks and performance issues.
To address this, API providers rely on API keys as a simple and effective way to control access and monitor usage.
What are API Keys?
An API key is a unique string assigned to an application that requests access to an API.
It identifies the calling system rather than an individual user, allowing the provider to recognize who is making each request.
Generated by the API provider, the key is included in API requests and used as a basic authentication mechanism.
It helps verify the source of the request and determine what level of access or usage is allowed.
How API Keys Help Manage and Control Access?
API providers rely on these keys to distinguish between thousands of unique clients and ensure only registered applications reach specific resources.
They provide the necessary telemetry to track usage patterns for billing and business intelligence while enforcing rate limits to prevent server overloads.
Application Identification
Beyond simply knowing "who" is calling, identification allows providers to segment their user base.
For example, a service might distinguish between a mobile app, a web dashboard, and a background cron job , all owned by the same company but using different keys.
This granularity helps developers debug issues specific to one platform without sifting through logs from every other part of their infrastructure.
It also allows providers to offer tailored support by seeing exactly which version of a client application is triggering errors.
Access Control
Access control through API keys serves as a granular management layer that dictates exactly what a client can do once they are inside the system.
Instead of a simple "all-or-nothing" permission structure, providers link each key to a specific "Permission Manifest" that outlines authorized actions and data boundaries.
Read vs. Write
Providers use keys to enforce granular permissions, such as allowing a partner to view product inventory while strictly blocking them from changing prices or deleting records.
This "Read vs. Write" restriction protects data integrity and limits the potential damage if a key is intercepted.
By defining these boundaries, you ensure that third-party integrations can only perform the specific actions required for their role.
Service Tiering
Organizations leverage API keys to gate-keep premium features, allowing them to offer different service levels based on the user's subscription or partnership.
A basic key might provide access to standard data endpoints, while a "Gold" tier key unlocks advanced analytics, real-time updates, or significantly faster processing speeds.
Usage Monitoring
For an API provider, data is a product. API keys provide the telemetry needed to understand how that product is consumed.
By tracking key usage, providers can perform Trend Analysis to see if a particular feature is becoming obsolete or if a new endpoint is gaining traction.
This business intelligence informs the roadmap for future updates.
Furthermore, it allows for resource attribution, which is vital in large corporations to track which department is consuming the most cloud resources and should be billed accordingly.
Rate Limiting
Rate limiting is a protective measure against the "noisy neighbor" effect.
Without keys and limits, one poorly written loop in a single developer's code could send millions of requests a second, overwhelming the server and causing a blackout for all other users.
Quota Management
Quota management allows providers to set specific usage "buckets," such as 5,000 requests per month, to ensure fair resource distribution across all clients.
By linking these limits to an API key, the system can automatically throttle or block traffic once a threshold is reached, protecting the infrastructure from unexpected spikes.
This structure also enables businesses to offer scalable service plans, where higher-tier keys unlock larger request volumes for enterprise-level needs.
Burst Control
Burst control acts as a real-time safety valve by limiting users to a strict number of requests per second, such as 5, regardless of their total monthly allowance.
This granular restriction prevents sudden traffic spikes from a single user from overwhelming the server or degrading performance for others.
By enforcing these short-term limits, providers ensure the entire API ecosystem remains responsive, stable, and fair for all connected applications.
Security
In the event of a security breach such as a developer accidentally committing their key to a public GitHub repository the provider can instantly revoke that key. This immediately neutralizes the threat.
Since the keys are unique, the provider can shut down the compromised account without affecting thousands of other innocent developers.
Additionally, keys help in Audit Logging, providing a forensic trail that security teams can use to investigate which account was used to access sensitive data during a breach.
How API Key Authentication Works?
The technical execution of an API key follows a predictable cycle that balances speed with security.
This four-step process begins with the provider generating a unique string that acts as a digital fingerprint for a specific project.
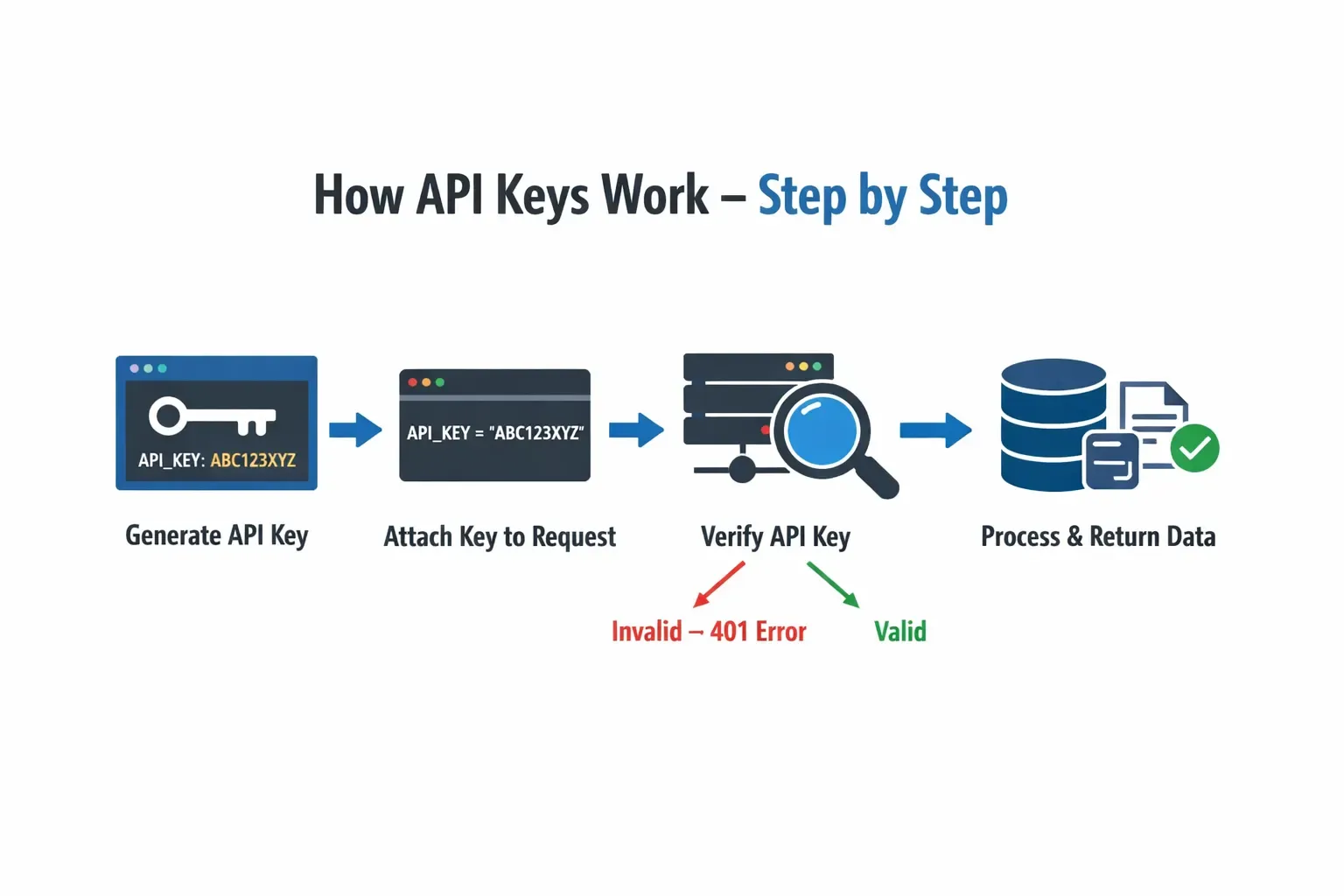
Step 1: Generation and Assignment
The process begins in the API provider's developer console. When a developer creates a new project, the provider generates a unique key.
Behind the scenes, the provider stores this key in a secure database, linked to the developer’s account, billing information, and permission levels.
Step 2: Client-Side Integration
The developer takes this key and stores it within their application environment. In a modern full-stack application, the key is typically kept in an environment variable.
When the application needs to make a call, the code retrieves the key and attaches it to the outgoing HTTP request.
Step 3: Verification at the Edge
When the request arrives at the API gateway or server, the system pauses to inspect the credentials.
The server looks for the key in the expected location usually the request headers. It then performs a lookup in its internal cache or database.
If the key doesn't exist, the server returns a 401 unauthorized status.
Step 4: Logic Execution and Response
Once the key is verified, the server checks the "quota" associated with it.
If the application has made 999 requests out of an allowed 1000, the request is allowed through, and the counter is updated.
Finally, the server processes the requested logic such as querying a database or generating a report and sends the payload back to the client.
How API Keys Are Applied Across System Integrations
The implementation of API keys is foundational to how modern software ecosystems operate, serving as a bridge between separate platforms.
Whether used for external integrations or internal tracking, these keys allow developers to turn isolated applications into interconnected tools.
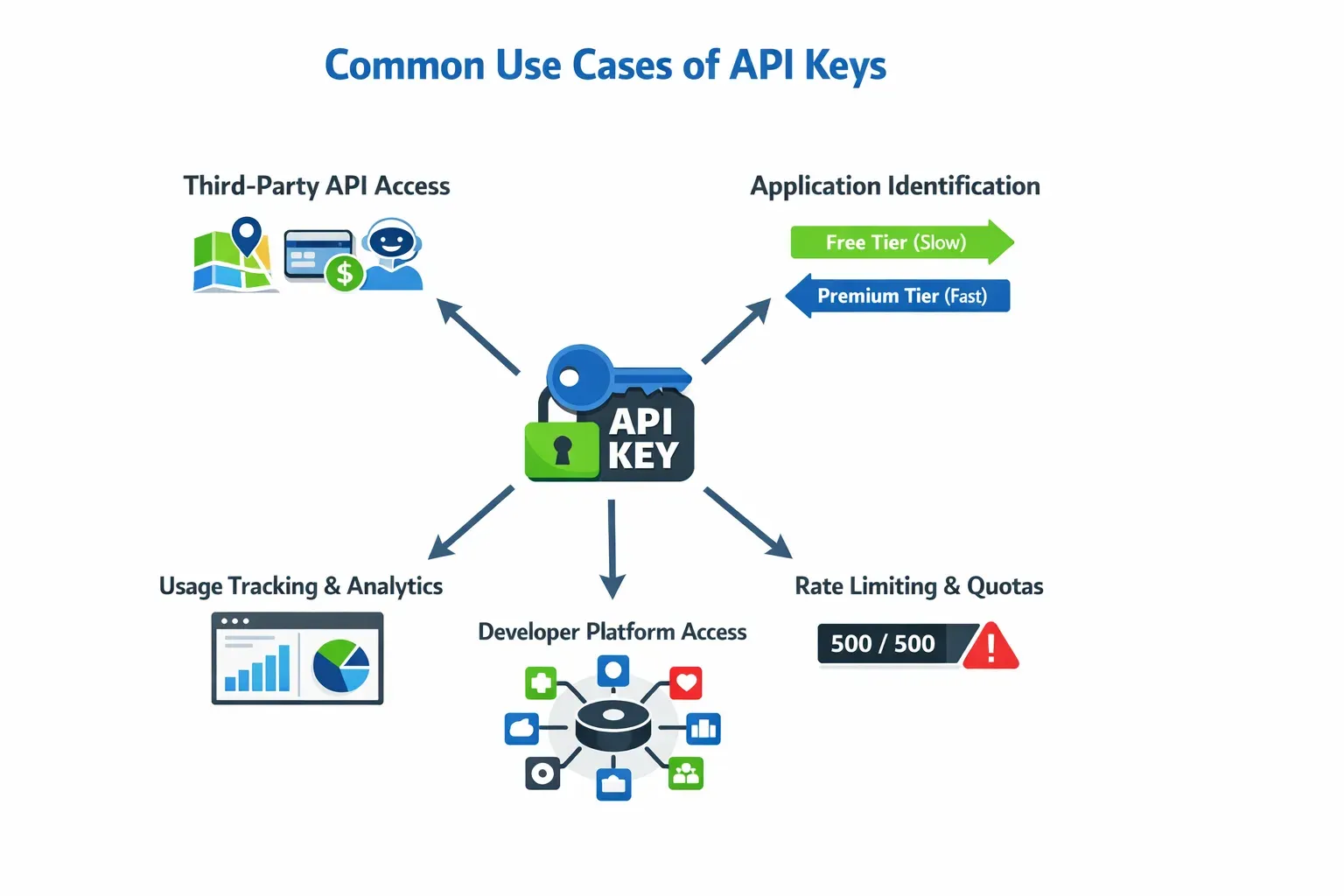
Third-Party API Access
Most developers first encounter API keys when integrating specialized external infrastructure into their own projects.
Using API keys issued by platforms like Google Maps, Stripe, and OpenAI, developers can extend their applications with specialized functionalities such as geolocation, payments, and AI-driven features without managing the underlying infrastructure.
In this scenario, the API key acts as a digital subscription ID.
It ensures that the provider knows exactly which account is requesting the data, allowing them to verify permissions and bill the developer accurately for the resources consumed.
Application Identification
API keys are frequently used to categorize and manage different versions or tiers of a software product.
For instance, a company might issue different keys to distinguish between a "Free Tier" mobile app and a "Premium Tier" enterprise dashboard.
This allows the server to dynamically adjust its behavior perhaps providing lower-resolution data or slower response times to the free key while unlocking high-frequency, high-resolution data for the premium key.
This identification also helps developers track which versions of their software are still in active use, making it easier to decide when to stop supporting older, outdated releases.
Usage Tracking and Analytics
For data-driven organizations, an API key is a vital tool for gathering business intelligence.
By assigning a unique key to every partner or client, a provider can generate a detailed map of how their service is being used.
These analytics reveal peak usage times, identifying exactly when the infrastructure is under the most stress, and highlight which specific features are the most valuable to the user base.
This level of tracking can even help predict user churn; if a key that was previously active suddenly stops making requests, it serves as an early warning that a partner may be moving away from the service.
Rate Limiting and Quotas
To maintain a stable environment for all users, API pry request to a specific API key, the system can instantly count how many calls a user has made.
If a user exceeds their daily quota of 500 requests, the server can automatically pause their access until the next window, ensuring that no single "noisy neighbor" can monopolize the shared system resources.
Developer Platform Access
Large software companies often grow into massive ecosystems by turning their product into a platform for others.
By offering a public API and issuing keys to outside developers, a company allows third parties to build entirely new tools, plugins, or integrations on top of their core service.
For example, a social media platform might provide API keys to developers building scheduling apps or sentiment analysis tools.
This strategy exponentially increases the overall value of the original service, turning it into a foundational layer for an entire industry.
What are the Benefits of Utilizing API Keys
API keys are favored by developers primarily for their balance of functionality and ease of use.
They provide a foundational layer of management that is both accessible for beginners and effective for high-traffic services.
Simplicity of Implementation
Integrating API keys requires very little code compared to more complex systems. Developers can get an authenticated connection running by simply including a string in a request header, avoiding the need for intricate libraries or multi-step handshake protocols.
Low Computational Overhead
Because verifying a static string is a straightforward database or cache lookup, API keys are incredibly fast.
This makes them ideal for high-frequency requests where adding a heavy authentication layer would increase latency and slow down the user experience.
Built-in Usage Attribution
Every request made with a key is automatically tied to a specific project. This provides immediate clarity on which applications are consuming resources, allowing providers to generate accurate billing and detailed analytics without manual tracking.
Automated Quota Enforcement
API keys provide a native way to manage server traffic. Providers can set hard limits on how many requests a key can make per minute or month, protecting the infrastructure from being overwhelmed by a single malfunctioning or malicious client.
Ease of Revocation
If a specific application behaves poorly or its security is compromised, the provider can invalidate that single key.
This acts as a targeted kill-switch, allowing the provider to stop a threat instantly without disrupting service for any other authorized users.
Security and Operational Limits of API Keys
While API keys are efficient, they possess inherent structural weaknesses that make them unsuitable for every security scenario.
Lack of Individual User Identity
An API key identifies the application, not the person using it. If a developer needs to know exactly which human user is acting, an API key cannot provide that information; it only confirms that the request came from an authorised software project.
Vulnerability to Exposure
Since API keys are simple strings, they are easily leaked. If a key is accidentally hard-coded into a public GitHub repository or intercepted over an insecure connection, an attacker can use it immediately.
Once a key is out, it is essentially "bearer" credentials whoever holds it has full access.
No Inherent Expiration
Unlike modern tokens that expire after a few minutes or hours, API keys are generally permanent until manually deleted.
This long lifespan means that a compromised key can remain a silent security hole in a system for years if the developer does not practice regular rotation.
Static Permission Structure
Most API keys offer an "all-or-nothing" approach to permissions. They often lack the granular control found in protocols like OAuth, which can limit access to specific data fields or time-limited actions, making keys a blunt instrument for complex security needs.
Susceptibility to Man-in-the-Middle Attacks
If a request is sent over an unencrypted HTTP connection, an API key is visible in plain text.
Without the additional layers of encryption and digital signatures used by more advanced methods, the key is highly vulnerable to being "sniffed" or stolen during transit across the network.
Best Practices to Manage API keys Securely
To keep your application safe, follow these rules: prioritize storing credentials in environment variables rather than hard-coding them into source files to prevent accidental leaks.
Additionally, implement periodic key rotation and enforce IP or domain restrictions to ensure that even a compromised key has a limited window of misuse.
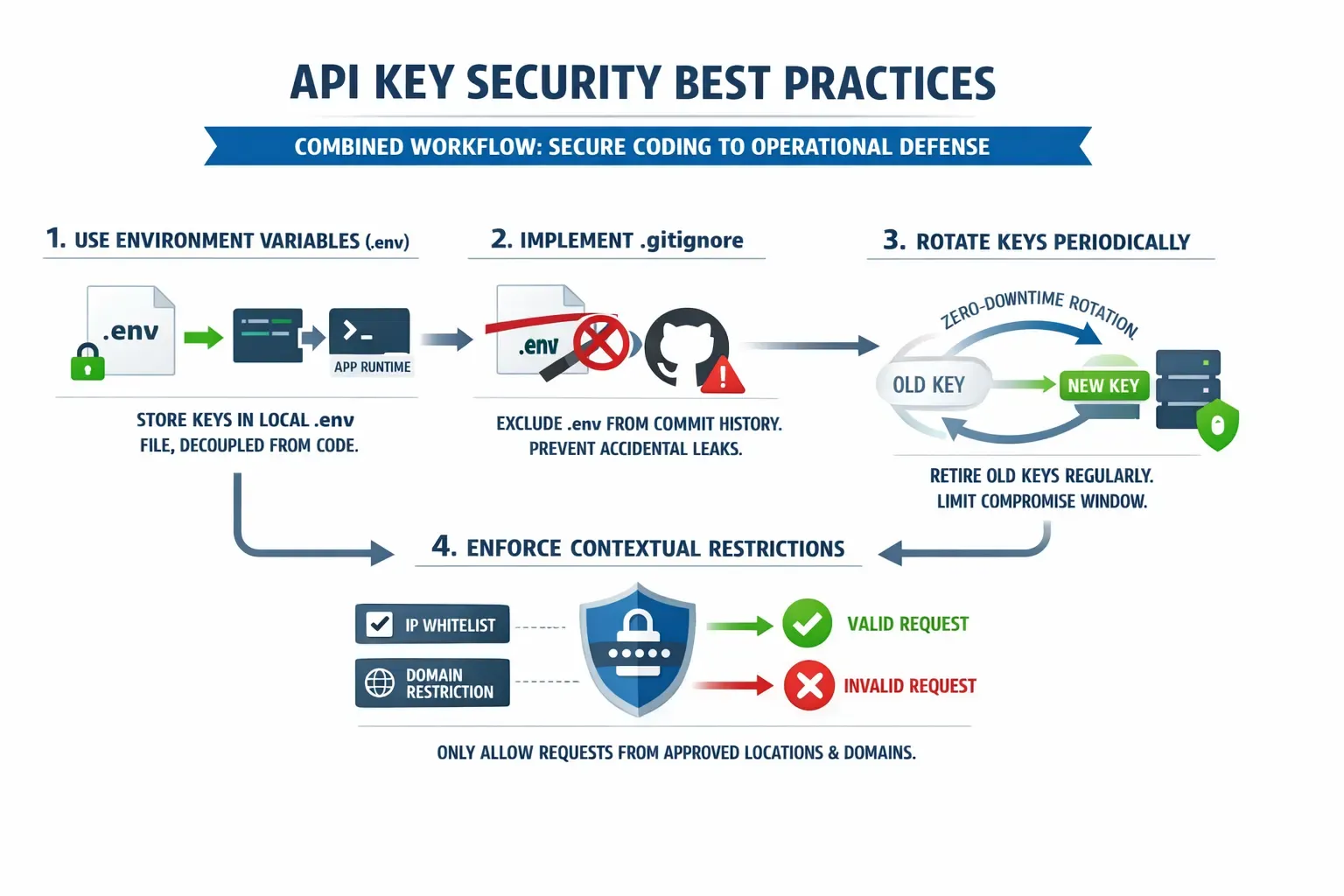
Keep Them Private
Hard-coding occurs when a developer types a sensitive string directly into a variable within a .js, .java, or .py file.
While this is the easiest way to get a project running, it is the most dangerous.
If that code is committed to a version control system like GitHub, the key becomes part of the repository's history.
Even if you delete the line in a later commit, the key remains visible in the "commit history" to anyone with access to the repo.
Bots constantly scan public repositories for these strings, often finding and exploiting leaked keys within seconds of a push.
Use Environment Variables
Professional developers use Environment Variables to store sensitive API keys in a .env file, ensuring they are decoupled from the application logic.
Gitignore
To implement this correctly, you must utilize a .gitignore file to explicitly exclude your .env files from being tracked by version control systems like Git.
This step is non-negotiable in a professional workflow, as it prevents your private keys from being pushed to shared or public repositories where they could be harvested by automated scripts.
By keeping the keys local to the environment and the logic in the repository, different team members can use their own unique keys for testing without ever risking a leak of the production credentials.
Rotate Periodically
Key rotation is the practice of retiring an old API key and generating a new one at regular intervals.
If a key was silently compromised without your knowledge, an attacker only has a limited window of time to use it before it expires.
Most major API providers allow you to generate a second key while the first is still active, enabling a "zero-downtime" transition where you update your server with the new key before deleting the old one.
Restrict Permissions
Many modern API providers allow you to add a layer of "Contextual Security" to your keys. Even if an attacker steals your key, they cannot use it unless they are making the request from an approved location.
IP Whitelisting
You can tell the provider to only accept requests coming from your specific server's IP address.
Comparing API keys with Modern Approaches
While API keys are great for "Project-to-Server" communication, other methods are better for "User-to-Server" tasks:
Challenges of managing API keys at scale
When a service expands to accommodate thousands of global partners, the sheer volume of unique identifiers makes manual oversight impossible.
Organizations must move beyond basic authentication and into a structured ecosystem where every key is treated as a managed asset with its own lifecycle, health metrics, and security profile.
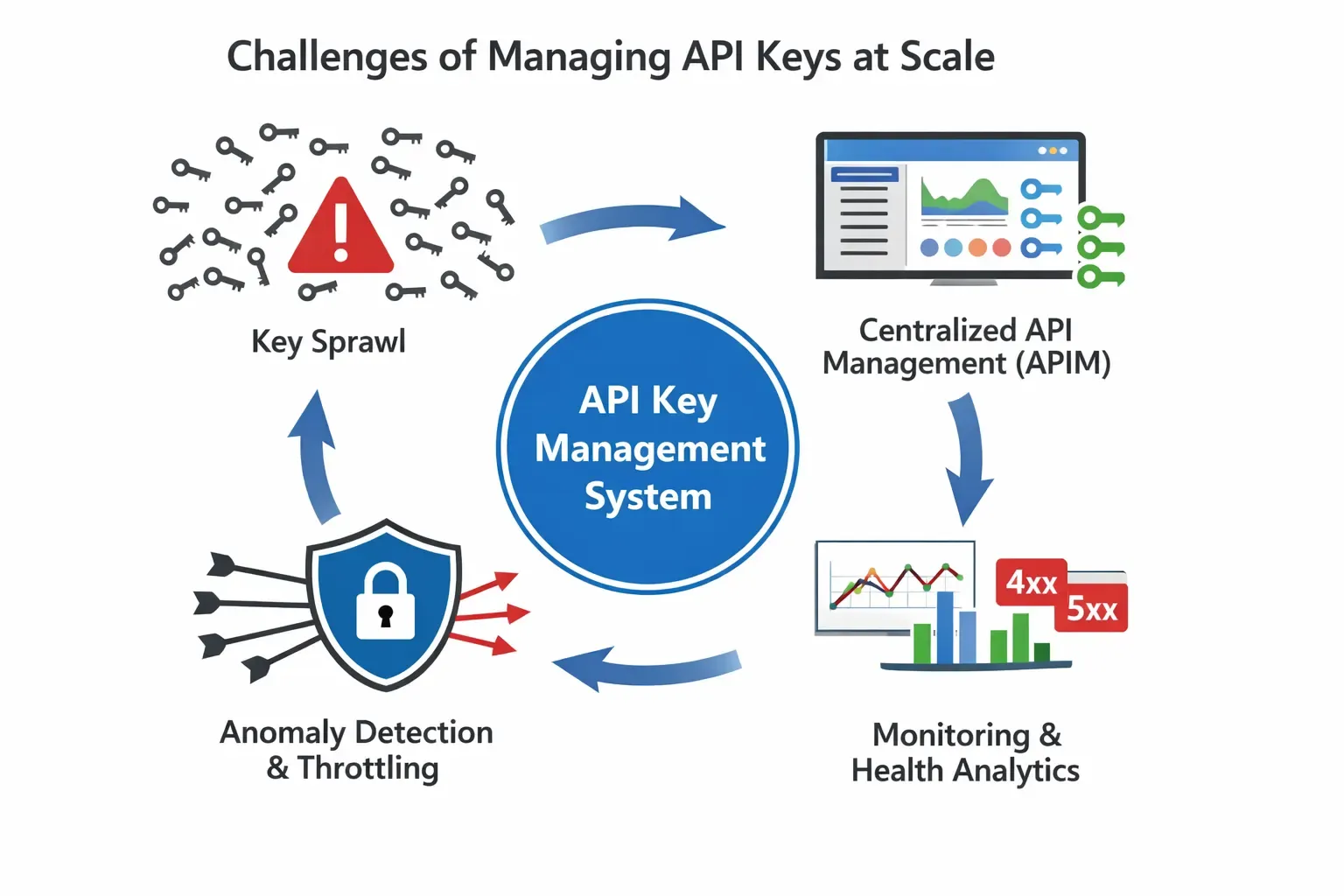
1. The Operational Burden of Scale
The primary challenge of growth is the transition from managing a handful of keys to overseeing thousands of individual partner integrations.
As the number of partners reaches figures like 5,000, it becomes increasingly difficult to track who owns which key, what data they are authorized to access, and whether their integration remains active.
Without a centralized system, the organization risks "key sprawl," where orphaned or forgotten keys remain active, creating significant security vulnerabilities and making it nearly impossible to audit system access effectively.
2. Centralized Governance via API Management
To combat this complexity, large-scale systems utilize API Management (APIM) platforms that serve as a centralized control plane.
These platforms provide administrators with comprehensive dashboards that aggregate data across the entire partner network, allowing for "at-a-glance" monitoring.
Instead of digging through raw server logs, teams can use these tools to identify which keys are nearing their assigned quotas, which are experiencing high error rates, and which have become "zombie keys" those that have not initiated a request in months and should be decommissioned to reduce the attack surface.
3. Proactive Monitoring and Health Analytics
Beyond simple connectivity, scaling requires a deep understanding of the "health" of each partner's integration.
Monitoring at this level involves tracking performance patterns to catch issues before they lead to system-wide failures.
For example, if a specific partner key begins showing a high rate of 4xx or 5xx errors, it may indicate a version mismatch or a broken implementation on the partner's side.
API management tools allow teams to proactively reach out to partners to resolve these technical friction points, ensuring the overall reliability of the global service.
4. Automated Anomaly Detection and Protection
The most critical aspect of managing keys at scale is the ability to react to sudden, unexpected changes in traffic patterns.
High-traffic environments are susceptible to "noisy neighbor" effects, where one partner's runaway script or technical glitch consumes all available system resources.
Modern management platforms use automated anomaly detection to establish a baseline of "normal" behavior such as 10 requests per hour.
If that key suddenly spikes to 10,000 requests per second, the system can automatically trigger throttling or a "circuit breaker" to isolate that specific key, protecting the infrastructure's stability for the remaining 4,999 partners.
Complete API Functionality Breakdown Using an E-commerce Application
Imagine a brand let's call it NovaSkin selling 200+ skincare products on their own website, plus Amazon and Nykaa.
Every time a customer buys, searches, or reviews a product on any of those platforms, a web of APIs is working in the background. Here's exactly how it all fits together.

Every arrow in that diagram is an API call, and every API call needs a key , a credential that identifies who is making the request and what they're allowed to do.
Now let's walk through each API, what it does, and what happens under the hood.
API 1
Product Catalog API (Product Website)
When NovaSkin adds a new serum to their catalog, a single API call pushes it everywhere.
Here's the exact flow:

The product catalog API call typically looks like this in practice:
POST https://api.novaskin.com/v1/products
Authorization: Bearer sk_live_NovaSkin_XXXXXXXX
Content-Type: application/json
{
"sku": "NS-SERUM-VIT-C-30ML",
"name": "Vitamin C Brightening Serum 30ml",
"price": 899,
"currency": "INR",
"stock": 500,
"images": ["https://cdn.novaskin.com/ns-serum-vitc-main.jpg"],
"category": "serums",
"description": "..."
}The API key (sk_live_NovaSkin_XXXXXXXX) is what tells the server: this request comes from an authenticated NovaSkin admin, not a random person on the internet. Without it, the server returns 401 Unauthorized.
API 2
Inventory Sync API
This is the one that saves NovaSkin from overselling. When stock drops to zero on Amazon, it must also update on Nykaa and their own site within seconds.

API 3
Order Management & Payment API
When a customer buys on novaskin.com, the checkout triggers a sequence of API calls in under two seconds:

Notice the HMAC signature verification step ,this is how NovaSkin's server knows the webhook genuinely came from Razorpay and not a malicious actor faking a payment notification.
The API key signs the payload; NovaSkin re-computes the hash and compares it.
API 4
Image & CDN API (Cloudinary)
NovaSkin has 200+ products, each needing different image dimensions: Amazon requires 2000×2000px white background, Nykaa wants 800×800, their own mobile app needs a 400×400 thumbnail. One upload, one API call, all formats:
// Upload once — Cloudinary API auto-generates all variants
const result = await cloudinary.uploader.upload('serum_raw.jpg', {
public_id: 'ns-serum-vitc-30ml',
transformation: [
{ width: 2000, height: 2000, crop: 'pad', background: 'white' }, // Amazon
{ width: 800, height: 800, crop: 'fill' }, // Nykaa
{ width: 400, height: 400, crop: 'thumb' } // Mobile
]
});
// API returns: { secure_url: "https://res.cloudinary.com/novaskin/..." }The API key here (CLOUDINARY_API_KEY + CLOUDINARY_API_SECRET) lets Cloudinary know which NovaSkin account to bill and which transformations are allowed.
API 5
Reviews & Ratings Sync API

Every one of these integrations relies on an API key. Here's exactly what role the key plays at each step:

Full API Key Map used in Above
The Razorpay key never touches the browser , this is the critical rule. The secret that signs payments lives only on NovaSkin's ( Client) server. Expose it in frontend JavaScript and anyone can create fraudulent orders.
What Breaks Without API Keys
If NovaSkin's Amazon key expires or gets rotated without updating the integration , the inventory sync stops silently, Amazon listings go stale, and within hours customers start placing orders for items that are out of stock.
The API key isn't just authentication ,it's the living connection between NovaSkin and every platform they sell on.
Summing Up
API keys provide a simple, lightweight, and effective way to manage how applications interact. They bridge the gap between having no security and having an overly complex authentication system. By identifying the caller, enforcing limits, and providing a way to revoke access, they give developers the control needed to run a professional service.
For developers currently building full-stack applications, the focus should remain on invisibility: the key should be present in every request but never visible in the code. By combining API keys with secure storage and scoped permissions, you can ensure that your application remains a safe and reliable part of the digital ecosystem.
