Top IoT Cloud Platforms and How to Choose the Right One
.jpg&w=3840&q=75)
What Are IoT Cloud Platforms?
The Internet of Things (IoT) is a physical object, like a sensor, industrial equipment, vehicles, or another consumer product with an internet connection.
The gadgets produce continuous operational data streams that organizations use for their monitoring, automation, and analytics.
Devices are, however, not sufficient. They require a central authentication system that is secure and ensures data exchange, telemetry storage, and integration with business applications, similar to patterns seen in cloud-native application development on Google Cloud environments. IoT cloud services are what come in at this point.
The IoT cloud platform is a cloud-based platform that is specifically created to communicate, manage, and handle data of IoT devices.
It includes pipelines used to ingest data, storage, analytics integration, messaging (including MQTT or HTTP), and device identity management.
Rather than constructing this infrastructure directly, managed IoT cloud providers are used by organizations to manage device fleets and coordinate the flow of data between systems.
The increasing dependency on centralized IoT infrastructure is demonstrated in terms of investment in the market. As SNS Insider reports, in 2024, the market of IoT cloud platforms across the world was estimated at around 23.26 billion and will grow to reach 71.7 billion in 2032.
This development signifies the fact that companies are progressing toward more than mere connection of the devices and into organized IoT cloud solutions to operate device fleets, assure information sharing, and interface the IoT activities with business operations.
With the increase in deployments, cloud Internet of Things solutions are no longer considered to be consultation features.
How IoT Cloud Platforms Work
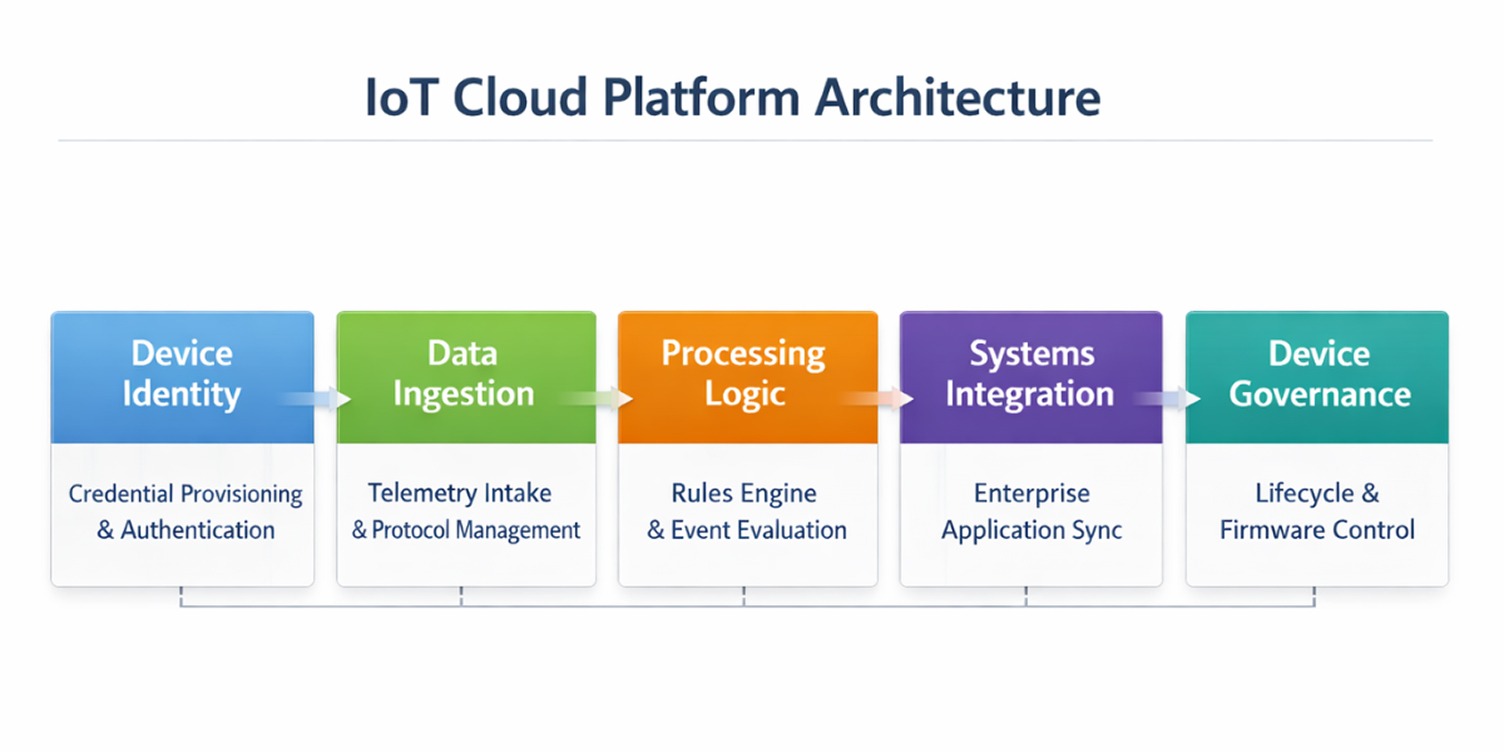
An IoT cloud platform at an architectural level deals with three fundamental tasks: creating safe connections between devices, organizing the processing of incoming data, and coordinating the flow of the latter into operational systems.
This flow is essential to consider when analyzing an IoT cloud platform, as architectural disparities have a direct impact on performance, security posture, and long-term maintainability.
Global Secure Access and Identity of devices
Each device has to be distinctly identifiable. The platform provides credentials in the process of onboarding, authenticating every connection request through structured cloud security and identity management practices.
This avoids the occurrence of unauthorized endpoints that may be injecting data or issuing commands.
Identity management can not be scaled down. In its absence, organizations do not have visibility on the devices that are active, outdated, or compromised. Mature IoT cloud providers are characterized by strong identity controls.
Messaging and Data Intake
Upon authentication, devices send telemetry using lightweight protocols, e.g., MQTT or HTTP. These messages come to the platform via controlled endpoints that are high-throughput ingestion.
This intake layer is necessary to validate, impose a communication policy, and ensure device data flows through structured pipelines rather than being dispersed across unrelated systems, a common requirement in distributed backend environments.
Decision Logic Processing
Inbound information is not transferred to dashboards. It is assessed initially in the platform. Processing services or rules engines are used to decide whether the data needs to be stored, redirected, or processed to cause an attempt at some operational response.
When implementing an industrial IoT, sensor data can be compared to performance levels in real-time. In the presence of deviations, the platform is able to start the maintenance process or create alerts. It is this logic layer that makes the difference between an application-specific IoT cloud platform and a simple cloud storage.
Operational Systems integration
The usefulness of an IoT cloud service is determined by its ability to interact with the rest of the technology stack in an organization. Processed device data has to be combined with enterprise applications and analytics systems (or customer-facing platforms).
High integration functionality enables IoT data to be no longer merely monitored, but also used in operational decision-making. This is commonly an influencing factor when comparing IoT cloud platforms.
Ongoing Device Governance
Developments keep them out there for years later. As time passes, they need to be configured, credentials switched, firmware updated, and performance monitored. These controls are concentrated on the platform.
Devoid of a formal platform for managing the IoT devices, organizations would stand to be faced with the peril of dispersed management and increased vulnerability in their operational aspects, with an increase in the number of devices.
These architectural layers are more significant than feature lists compared to the comparison between the IoT cloud platforms. The power of device identity policies, ingestion pipelines, integration possibilities, and lifecycle management would help decide whether a deployment could be managed as it scales.
Best IoT Cloud Platforms Compared
The IoT cloud platforms do not vary as much in the basic connectivity capabilities as much as it varies in the architectural orientation, which is normally a reflection of the overall enterprise cloud infrastructure strategies that already exist in an organization.
The actual dividing lines are the ecosystem-alignment, edge-strategy, device fleet maturity, pricing action, and industry specialization.
The majority of platforms can be divided into two categories: hyperscale cloud providers that have expanded to the IoT, and industrial platforms that are built on operational technology environments.
Hyperscale IoT Cloud Platforms
Hyperscale providers are preferred where the IoT needs to be closely coupled to cloud native workloads like analytics pipelines, event based compute and enterprise identity systems.
AWS IoT Core
AWS IoT Core is designed with high-throughput messaging and extensive integration with the rest of the AWS stack. The telemetry of devices would be a natural fit in services like Lambda, S3, DynamoDB, and Kinesis, which would fit event-driven architectures and data-intensive environments.
The core of its edge strategy is AWS Greengrass, which enables some workloads to be placed nearer to the devices and synchronize with the cloud. This helps in the hybrid deployment,s but the architecture is cloud-first. Companies with heavy AWS infrastructure are frequently discovered to integrate IoT loads with few struggles.
Pricing works largely on the basis of the volume of messages and data transfer. In a middle level, expenses are reasonable. Forecasting is important at high-frequency telemetry rates. The message amplification because of shadow updates, rules triggers, and downstream services is one of the underestimates of many teams.
The tradeoff is the coupling to an ecosystem. Multicore architectures relying heavily on the AWS-native services may prove hard to implement in a multi-cloud strategy.
AWS IoT Core is also more likely to prevail in cloud-native deployment scenarios in which telemetry needs to be part of serverless and analytics pipelines constructed around cloud-native infrastructure strategies.
Azure IoT Hub
Azure IoT Hub is commonly chosen in companies that are standardized on the Microsoft infrastructure. Its compatibility with the Azure Active Directory gives it centralized control over both devices and users, which is especially useful in controlled settings.
Azure IoT Edge makes Azure's edge more pronounced than that of AWS. It enables a containerized workload to be executed by a gateway or edge device, which is ideal in a distributed industrial environment where local processing is needed.
Azure is more focused on enterprise governance and hybrid deployments than on event-driven telemetry scaling, as is the case with AWS. The pricing is also based on the message units and tiers of the services, which may offer a more predictable budgeting at the mid-scale level, but still require planning at very high volumes.
Companies that are strongly Microsoft ecosystems tend to adopt Azure IoT Hub as it integrates the current governance and identity models into the deployment of IoT applications.
Google Cloud (IoT via Cloud integrations)
Google Cloud does not offer an independent managed IoT core service anymore. Rather, services like Pub/Sub, Dataflow, and Cloud Run are used to assemble the IoT architectures with third-party device management solutions frequently.
This practice passes the burden to the engineering teams. Instead of implementing a dedicated IoT control plane, teams implement microservices design patterns of pipelines designed to be ingested, processed, and analyzed.
The area that Google differentiates is in the massive data processing and machine learning integration. This flexibility can be beneficial in the case of analytics-based IoT deployments. It does not, however, have the prepackaged device fleet management layer of AWS IoT Core or Azure IoT Hub.
Pricing is also based on the usage of various services as opposed to one IoT product, which can complicate cost modeling.
The Google Cloud IoT architectures are generally attractive to institutions with higher priorities in advanced data pipelines rather than turnkey device fleet management.
Oracle IoT Cloud
Oracle IoT Cloud is mainly used in the realm of asset management and supply chains. It is commonly compared with Oracle ERP systems as well as contrasted with AWS or Azure, not in head-to-head technical comparisons.
It is valuable because it adds telemetry to the organized enterprise operations. It does not emphasize hyperscale telemetry ingestion but matches IoT data to asset tracking, maintenance planning, and logistics operations.
Pricing and licensing would be based more on enterprise software models instead of being based on pure message-based billing. Consequently, it seems that evaluation is frequently integrated into larger digital transformation programs and not single engineering pilots.
Oracle IoT Cloud is not a cloud-native extensible solution but an enterprise process integration solution.
Enterprise and Industrial IoT Platforms
The IoT platforms in industry are constructed on operational technology as opposed to a cloud-native application stack. The integration with PLCs, SCADA systems, and industrial protocols like OPC UA and Modbus is their priority.
Consumer IoT projects are seldom selected on these platforms. They are found in manufacturing, energy, and utilities, and heavy equipment settings where architecture is based on the lifetime of equipment and continuity of its operation.
IBM Watson IoT Platform
IBM Watson IoT Platform is concentrated on the integration of analytics and hybrid cloud governance. It is commonly used in controlled industries where compliance and centralized control are of the essence.
Its power consists of linking IoT telemetry to enterprise analytics architectures instead of focusing on hyperscale message throughput. Watson IoT is included in a wider enterprise data strategy in organizations that already have IBM hybrid cloud infrastructure.
IBM does not emphasize event-driven cloud services in its differentiation, as AWS or Azure does but rather enterprise integration.
ThingWorx
ThingWorx is industrial-specific. It is used in the modeling of physical assets and is directly connected to the manufacturing systems.
Some of the features needed by industrial deployments are support of legacy equipment, industrial protocols, and equipment lifecycle visualization. ThingWorx satisfies these requirements by providing built-in digital modelling and integration manufacturing tools.
ThingWorx is based on equipment context and progressing towards analytics and visualization, unlike hyperscale platforms that modify cloud services to suit IoT.
It is usually used in connected product strategies and predictive maintenance initiatives enabled by systematized AI incorporation into the IoT systems.
Siemens MindSphere
MindSphere is an indicator of Siemens' industrial automation. It is closely implemented with Siemens control systems and factory equipment.
Under intelligent factory settings where Siemens hardware and automation systems have already been implemented, MindSphere can be extended to operational data into cloud-based analytics and monitoring systems, which allow an AI-driven transformation in the manufacturing process.
It is less common in general-purpose IoT deployments but highly relevant in industrial ecosystems where operational technology alignment determines platform selection.
Comparing the Major IoT Cloud Platforms
The comparison reinforces a simple reality IoT cloud platforms are not built with identical priorities. Some are engineered around large-scale cloud telemetry, others around enterprise control frameworks, and others around industrial system integration. Understanding that orientation matters more than checking feature lists.
IoT Cloud Platform Pricing and Cost Strategy
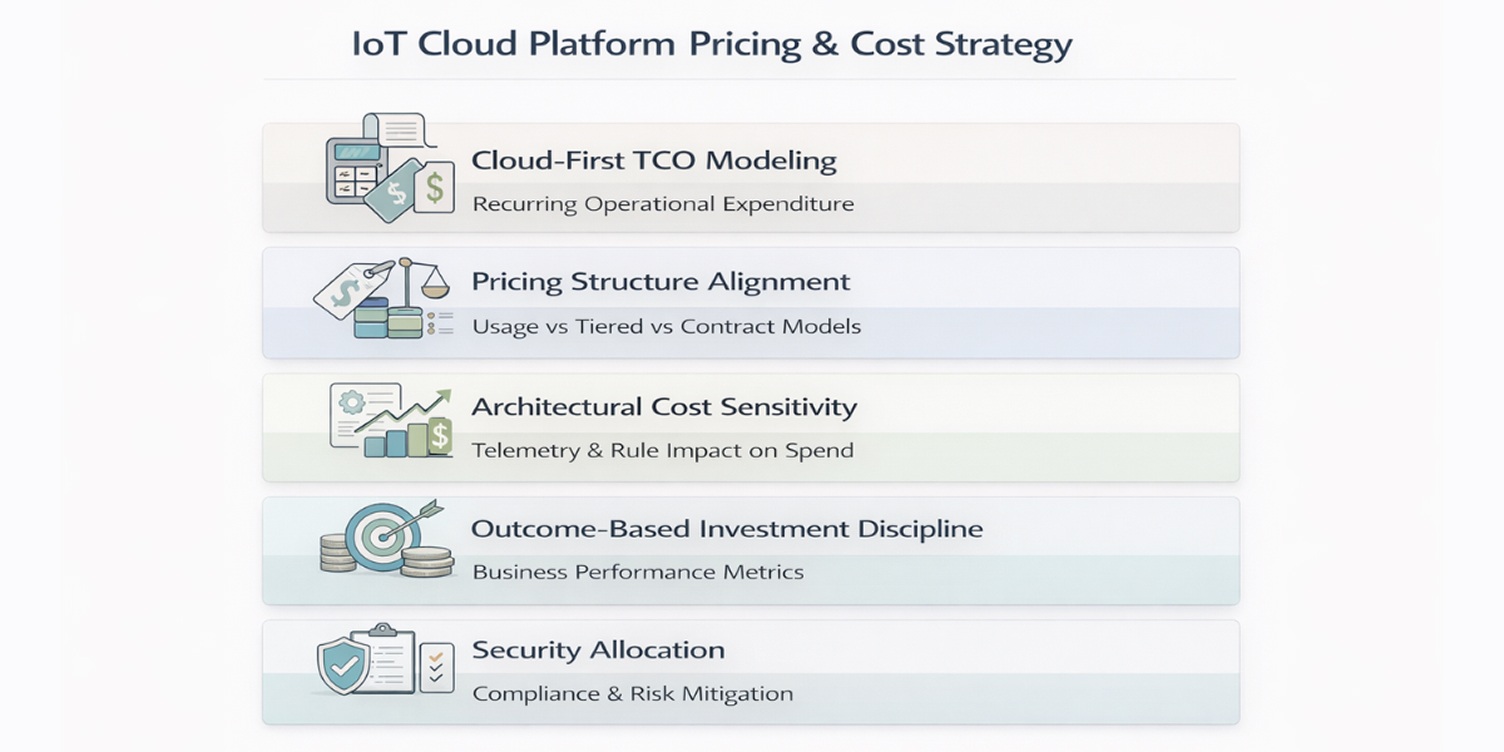
IoT cloud platforms are selected on technical capability, but sustained success depends on how the pricing structure and financial governance behave once fleets scale.
In production environments, commercial model and cost discipline matter as much as feature depth.
Cloud-First TCO Modeling
IoT cloud platforms introduce recurring cost layers that extend beyond deployment. Ingestion, processing, analytics workloads, integrations, and long-term storage create continuous operational expenditure.
In mature environments, annual cloud operating costs commonly reach 25–40% of the original implementation investment once fleets exceed pilot scale. In many mid-scale deployments, cross-service integrations and analytics pipelines eventually exceed pure ingestion charges.
Evaluating a platform without modeling this recurring exposure creates distorted budget expectations, especially when projected workloads are not validated under realistic conditions using appropriate load testing tools.
Pricing Structure Alignment
IoT cloud platforms generally operate under three commercial models: usage-based billing tied to message volume, tiered capacity bands with throughput thresholds, and enterprise contract structures based on deployment scale.
Each structure behaves differently at scale. Usage-based models respond directly to telemetry frequency and automation depth. Tiered models provide short-term predictability but introduce cost shifts when thresholds are exceeded.
Contract-based pricing reduces volatility but often increases long-term commitment, especially in environments that distribute workloads across multiple cloud providers and hybrid setups.
Platform selection should consider projected device growth and telemetry density rather than pilot-stage cost alone.
Architectural Cost Sensitivity
Financial exposure is shaped not only by the pricing model, but by architectural design.
Telemetry intervals, rule logic, integration depth, and data retention decisions influence recurring cloud expenditure. As device fleets expand, architectural adjustments can materially alter cost behavior.
In high-volume environments, small changes in reporting frequency or rule execution can produce disproportionate increases in monthly spend.
Cost discipline must therefore accompany architecture decisions before scale is increased.
Outcome-Based Investment Discipline
Funding IoT cloud platforms based solely on device count is insufficient. Mature deployments align investment with measurable operational outcomes, such as uptime targets, maintenance reduction benchmarks, or efficiency gains.
In connected product models, cost per active device directly affects subscription margin and long-term profitability. Financial evaluation, therefore, shifts from infrastructure expansion to business performance impact.
IoT cloud platforms should demonstrate sustained economic viability under real operating conditions.
Security Allocation as Financial Protection
Security and compliance readiness influence both operational stability and long-term cost.
Allocating 15–25% of development investment toward identity management, testing, and compliance validation reduces remediation risk after deployment.
Security underfunding in connected environments often results in significantly higher downstream correction costs, especially when regulatory audits or supply chain requirements are introduced post-launch.
Security & Compliance in IoT Cloud Environments
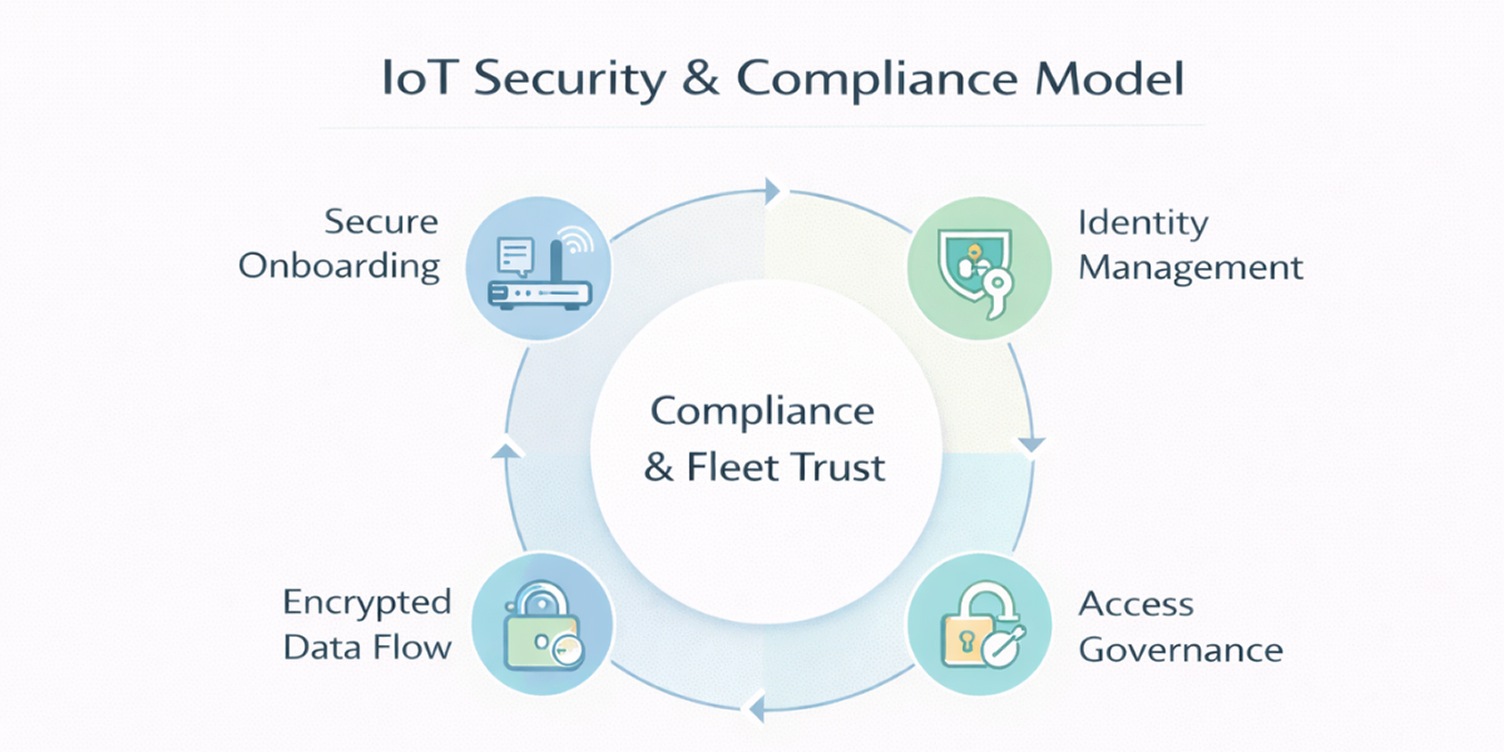
IoT cloud solutions increase the scope of cloud security. Each networked device is a remote system in continuous interaction with the cloud infrastructure.
The control of that interaction should be conducted by the use of identity control, encrypted communication, access segmentation, and aligning regulations.
IoT environments do not limit security to only the device layer or the cloud environment. It is present in the relationship between them.
Device Identity and Authentication Architecture
IoT cloud security is based on device identity. The mature platforms give every device a different cryptographic identity and do not use shared credentials or static keys. This enables authentication events to be followed, revoked, and rotated without impacting the entire fleet.
When deployments are at scale, the lifecycle of certificates becomes operationally important. It should be a platform that enables secure onboarding, identity rotation,n and revocation on command when devices are lost or destroyed. The most frequent point of entry in a big IoT setup is weak identity governance.
Identity architecture must not be considered as an afterthought when selecting the platform.
Data Protection Across the Device-to-Cloud Pipeline
Transport encryption is the norm between devices and cloud endpoints, but it is not sufficient to ensure it is safe. After telemetry gets to the cloud, it gets transferred to storage levels, analytics pipelines, and integration APIs.
These secondary layers are usually exposed. Even in the case of strong device authentication, misconfigured access controls, excessively broad permissions, or unsegmented data environments may pose a risk.
The IoT cloud platform is secure and implements the concept of access control in layers, limits the visibility of data in accordance with operational functions, and has a clear separation of ingestion services and application access interfaces.
Governance and Fleet-Level Access Control
The IoT implementations are in contrast to the conventional application since scale increases the risk. A policy error that is applied to a single device can impact thousands.
Powerful platforms offer fine-grained policy enforcement between groups of devices, implementation functions, and deployment conditions. The maturity of governance is seen in the ability of access rights to be defined, audited, and changed without interfering with production systems.
Access governance is a vital part of security posture in an IoT cloud environment,s just like encryption.
Regulatory and Compliance Readiness
The issue of compliance is becoming an important factor in the choice of IoT cloud platform, not only in the United States but also in foreign markets. Integrated systems should be used to provide audit logging, secure update processes, and traceable incident response procedures.
There is not only data privacy as a regulatory exposure. Connected products may have limitations on their operation due to industry-specific cybersecurity requirements and be subject to supply chain requirements.
In the case when a platform does not provide integrated compliance support, internal teams are forced to bear the burden, making the operation more complex.
The choice of an IoT cloud platform that has developed compliance tooling lowers downstream adaptation expenses.
Risk Allocation and Budgeting
The security of IoT is not over after the device onboarding. The update of firmware, alterations of configuration, and the process of decommissioning are to be implemented safely throughout the fleet.
MMs that are secure have signed firmware that has to be verified, controlled rollout methods, and have to be able to roll back in the event of failure. In the absence of lifecycle governance, vulnerabilities continue to exist in large populations of devices and are exponentially difficult to address.
Choosing the Right IoT Cloud Platform
Selecting the right IoT cloud platform depends less on feature lists and more on deployment context. Device scale, regulatory exposure, and economic model influence suitability far more than headline capabilities. The same platform can be optimal for one scenario and inefficient for another.
The following deployment profiles highlight how priorities shift across different IoT environments.
IoT Cloud Platform Fit by Deployment Type
Strategic Constraints That Shape Platform Decisions
The situation of deployment offers a sense of direction. The ultimate choice of platforms is, however, informed by the realities of operations that affect long-term viability.
Device Scale and Growth Horizon
The existing figure for the number of linked devices hardly gives the complete picture. Growth in the coming few years is projected to be more important.
A system that works well at pilot scale might not work as well when the volume of telemetry is increased. Trajectory should then inform the selection of the platform more than the size of the initial deployment.
Compliance and Regulatory Exposure
The level of governance should be in tandem with the industry requirements. In highly controlled environments, there is a need to have audit traceability, identity enforcement, and controlled update mechanisms, which are built into the platform architecture.
Underlying more straightforward compliance layers can create unwarranted operational overhead in less risky deployments.
Budget Tolerance Under Sustained Load
Continuous telemetry has varying responses to different IoT cloud pricing models. Companies that are not rigid about the variability of usage might enjoy the flexibility of billing schemes.
Other people might want to have cost envelopes that are predictable and offer less exposure to monthly changes. Platform suitability is directly proportional to financial posture.
Internal Cloud and Architecture Expertise
The needs of some IoT cloud platforms require proactive architectural management and integration. Modular flexibility can be used in teams that have mature cloud engineering capabilities.
Structured environments have the potential of benefiting organizations with limited internal expertise because they abstract complexity.
Vendor Dependency and Ecosystem Strategy
Intensive interconnection in a single cloud system will expedite the development and accessibility of services. But it also makes switching more and more complex. The choice of platform must be a trade-off between the speed of execution and the long-term flexibility of strategy.
Combining these variables, one can better understand the suitability of a platform than its features. The appropriate IoT cloud platform is resonant with long-term scale anticipations, governance necessities, financial tolerance, and internal capacity.
Cloud vs Edge vs Hybrid IoT Architectures
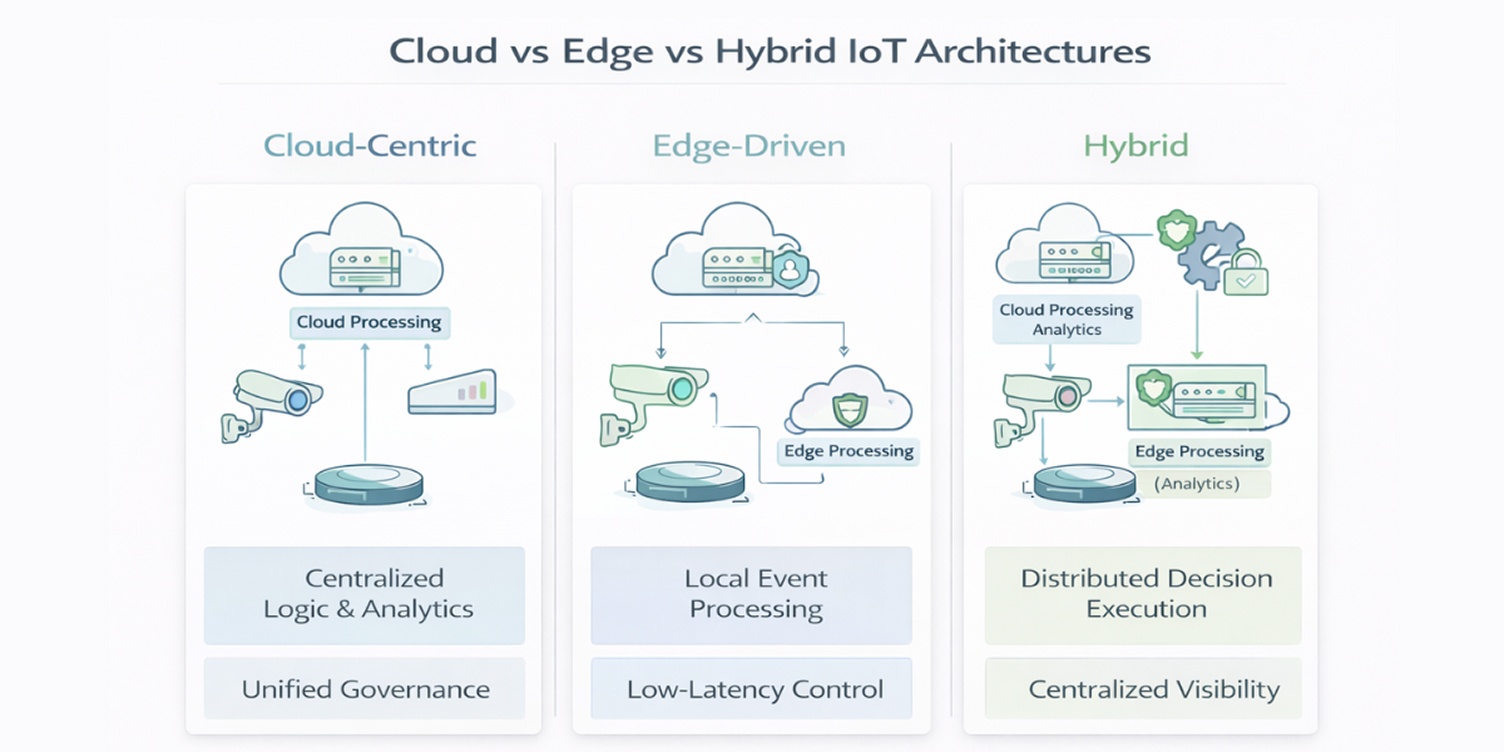
IoT cloud platforms are not separated. The architecture of deployment, be it cloud-based, edge-based, or a combination, has a direct bearing on the performance, latency tolerance, cost behavior, and governance needs.
The appropriate architectural model relies on the manner and position in which the decisions should be carried out.
Cloud-Centric IoT Architecture
In cloud first model, devices send telemetry straight to the cloud platform of the IoT cloud to be processed, stored, and analyzed. The major part of the business logic, automation rules, and analytics pipelines is implemented in the cloud.
This model makes it easy to manage the fleets and make the centralisation of governance. It is useful when the latency is not sensitive, and the connection is not a problem.
Consumer IoT, asset management, and connected products based on a subscription typically use cloud-based deployments where value is generated by a centralized analytics system.
Nevertheless, constant connectivity can reduce the appropriateness in distant or mission-critical settings.
Edge-Driven IoT Architecture
Edge-based design architectures bring processing units nearer to the device. Local data filtering, event detection, or control logic can be performed on data and sent to the cloud.
This will minimize bandwidth use and enable decision-making that is within a few seconds. Event-driven automation of industry, manufacturing, and infrastructure often needs edge processing in which milliseconds count.
The IoT cloud platform in such deployments plays the role of coordination and aggregation instead of being the only processing engine.
Hybrid IoT Architecture
A majority of IoT deployments that are done in the mature stage follow a hybrid model. Decisions are made at the edge, and long-term storage, analytics, and fleet governance are centrally stored in the cloud.
Latency control and centralized visibility. Hybrid architecture strikes a balance between latency and visibility. It allows companies to maintain business resiliency and, at the same time, use cloud-scale analytics and lifecycle management.
In the case of most enterprises, the hybrid design is a reality but not a choice.
Platform selection should not be substituted with architectural choice; it determines the way theIoT cloud platform is going to be utilized. Cloud-centric deployments should be supported on a powerful platform, and they should integrate well with the edge workloads where needed.
The most sustainable IoT plans consider platform capability alongside architectural requirements early on instead of adding edge support at scale.
